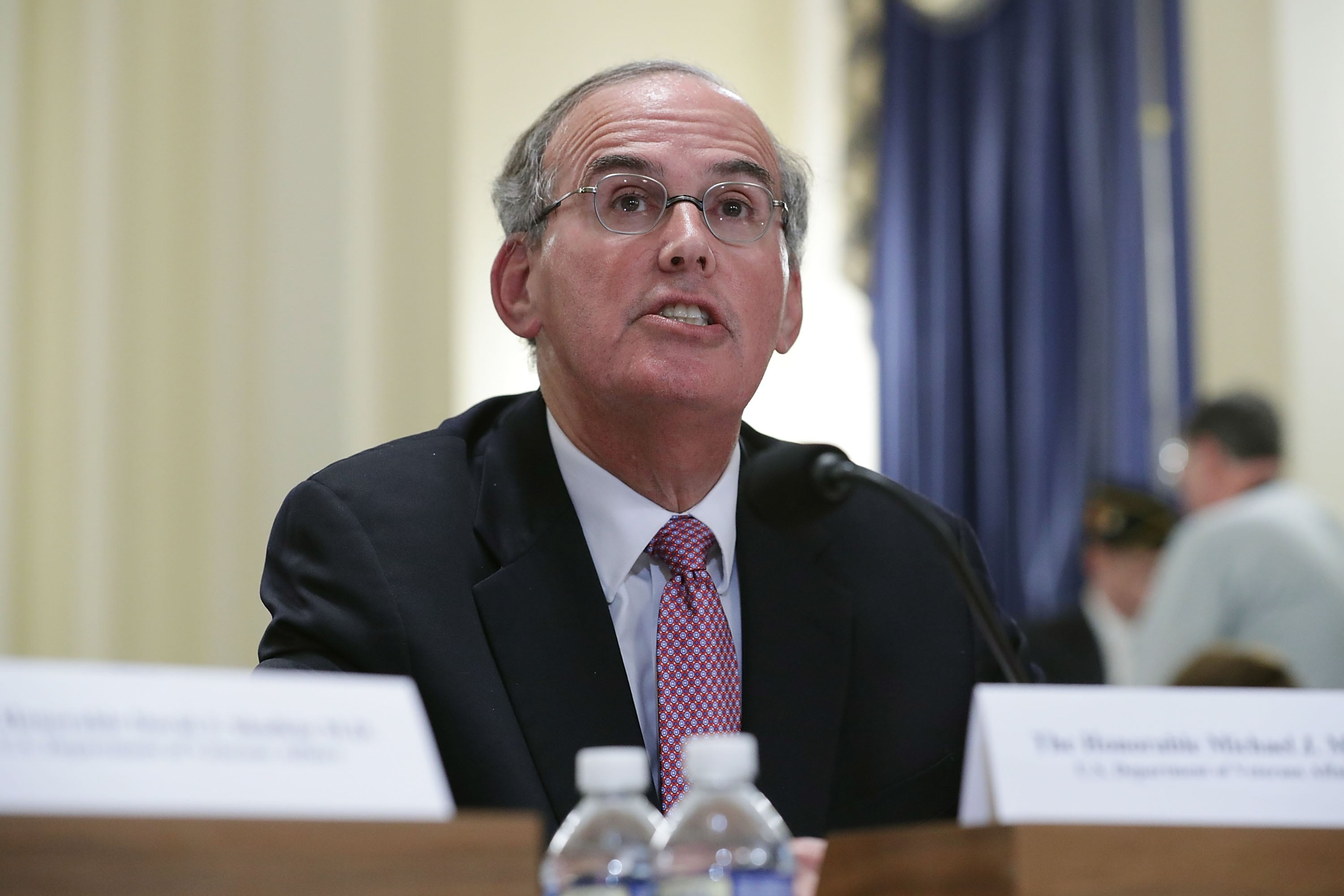
During an April 5 posture hearing into the work, the challenges and the future of U.S. Cyber Command, one of the consistent themes that emerged centered around manpower and how tomorrow’s cyber force will be built and maintained. Gen. Paul M. Nakasone, the head of the command, acknowledged those challenges and said one of his top five priorities is recruiting, retention and training.
Nakasone and many others in the Department of Defense correctly recognize these issues are key to correctly framing the problem. It is a mistake for the U.S. military to try and solve the problem of manpower and cyber capability by itself. This is not a departmental problem but one for the entire DoD. And while cyber is essential to many areas of DoD operations, it is not its main function.
RELATED
The DoD has cultivated a series of unique capabilities in defense of the U.S. and its borders. We have the best F-35 pilots in the world. But outside of Lockheed Martin and a few subcontractors, no commercial entity is flying the F-35. While we lead in executing missions of this kind, we must look to the commercial leaders excelling in technology to bring cybersecurity skills to the DoD. The DoD provides excellent training, professional development and valuable experience for certain skillsets. You must be a highly trained military pilot to fly a $135 million aircraft, but we are not producing the top talent in cyber, IT, training, staffing or experience. Modern war fighters need cyber in their arsenal.
The makeup of the U.S. digital landscape and infrastructure requires that every business maintain cyber security and capabilities across the spectrum. Military troops are more adept generalists because they must also maintain readiness and run our bases, ships and outposts. In comparison, commercial cybersecurity and technology professionals work full time in becoming subject matter experts. Beyond skills, this divide between civilian technologist and service member translates to a significant pay gap. A report this year estimated there are about 1.1 million people employed as cybersecurity professionals in the U.S., with an average starting salary range of $69,000 to $76,000 per year. The average annual starting salary for someone in the U.S. military is not even half that.
Considering Nakasone’s retention challenge within the military, money plays a part, but it is not the only factor. Army Times reported in 2019 that the Army raised bonuses for certain career fields from $72,000 to $81,000 — including cyber ops. Therefore, the choice to leave the military must be based on something other than money: the amount of time away from home, the lifestyle, rigid organizational structures, or other factors. What can be said is that people are leaving military service and going to work in the commercial world where they can earn higher salaries and have more flexible life choices. Our schools are also not producing lead candidates at the rate needed and employers are making up the difference with education and training benefits.
How do we address this cyber workforce problem? There is no luxury of time, as the DoD is under constant cyberattack, and large hacks such as SolarWinds and Colonial Pipeline are becoming more prevalent. The answer is to do what we are doing now, employ a mix of uniformed personnel, government civilians and contractors, but moving forward we must change how we allocate manpower and capability.
According to joint doctrine the missions of cyberspace operations are offensive operations, defensive operations and Department of Defense Information Network, or DODIN, operations. These three areas give a framework for where to put manpower and capability. Defense and DODIN are areas where we could have high concentrations of contractor employees and government civilians. Both groups would provide continuity and, on the contractor side, would be easier to scale as needed. The nature of offensive operations should be an area that has the highest concentration of uniformed personnel who are trained for this work. It would allow the commander to have the most control while building a trained and vetted force, with operations support conducted by those in defense and DODIN operations.
The offensive operators should have a firm grasp of how to execute their operations but also need to understand all aspects of cyber to include manpower and contracts. The offensive side of cyber operations will be a proving ground for the cyber leaders of tomorrow. Because cyber touches so many other warfare and commercial areas, the individuals who will lead tomorrow’s cyber fight must understand how many other disciplines and markets work. Cyber leadership should be trained on how government contracts work as well as how to quickly onboard commercial manpower into the command.
The men and women who have been defending our cyber borders have been doing an excellent job, but the enemy is relentlessly growing, learning and evolving. The cyber force of tomorrow should be agile, scalable and forward thinking. Invigorating the Defense Department with private industry veterans will bring the innovators, proven technology implementers, coders and software developers we need now. Partnering with private industry and government contractors will fill the human capital void, deliver proven talent and the necessary skillsets to protect our nation’s cyber frontiers and digital domain.
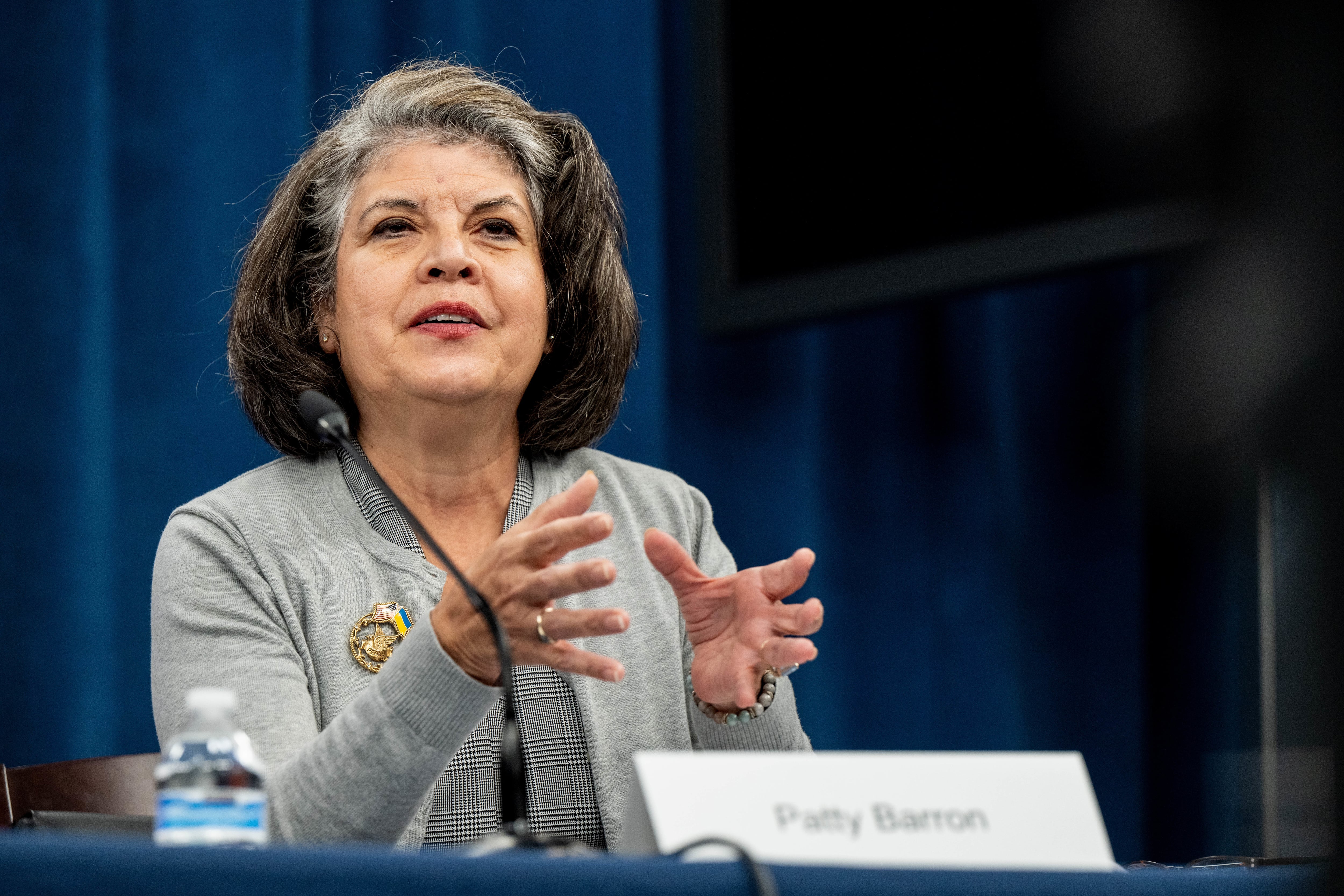
Retired Navy Capt. Larry Meehan is a senior advisor for The Roosevelt Group in Washington, D.C. After more than 30 years of service in the U.S. Navy, he retired from the Navy International Program Office where he served as the director of the Middle East Division. Meehan was also the commanding officer of Helicopter Sea Combat Squadron 8. He holds a master’s degree in public policy from American University and a bachelor’s degree in political science from the U.S. Naval Academy.
Have an opinion?
This article is an Op-Ed and as such, the opinions expressed are those of the authors. If you would like to respond, or have an editorial of your own you would like to submit, please email us.
Want more perspectives like this sent straight to you? Subscribe to get our Commentary & Opinion newsletter once a week.